A Cybersecurity Maturity Model for Cyber Deception Readiness
22 August 2022 | by Xavier Bellekens

What is a Cybersecurity Maturity Model?
A cybersecurity maturity model is a framework that organizations can use to assess their cybersecurity posture and identify areas for improvement. The model consists of a set of criteria against which an organization’s cybersecurity practices and capabilities are evaluated. The criteria are organized into levels, with each level representing a higher level of maturity. The criteria used in the model can vary depending on the specific needs of the organization. By using a cybersecurity maturity model, organizations can gain a better understanding of their strengths and weaknesses in relation to cybersecurity, and develop actionable plans for improvement.
With the Lupovis Cybersecurity Maturity Model, you can also assess whether you are ready to look at cyber deception solution.
What is cyber deception?
Cyber deception is a proactive cyber defense technique that uses bait to lure attackers away from an organization’s critical systems and data. By creating a deceptive environment, cyber deception can not only detect and block attacks, but also provide valuable information about an attacker’s tools, tactics, and procedures. Additionally, because cyber deception does not rely on signatures or knowledge of past attacks, it can be highly effective against zero-day exploits and other novel threats.
How does cyber deception help organizations?
Deception technology can help turn your network from a flock of sheep into a pack of wolves. By creating “lures” – false targets that attackers believe are real – you can then bait aversaries into revealing themselves and then track their every move. This informed awareness gives us the ability to shut down attacks before they do any damage.
Are you ready for cyber deception?
One way to detect attackers early, and waste adversaries’ time, is through the use of cyber deception. Cyber deception involves creating false targets within your network that will lead attackers away from your real data. However, before you can start using deception, you need to ensure that your organization is ready for it. Here is THE key factors to consider:
- Your Organization Maturity: Before you can effectively deceive attackers, you need to have the basics of security in place. This means, evolving from being a security practitioner into becoming a security investor!
With each step, the resources, processes and management practices will evolve.
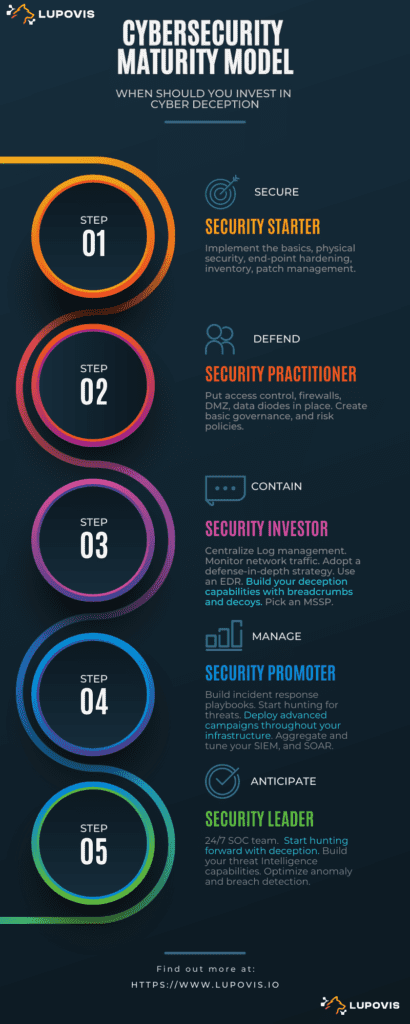
The two first steps of the cybersecurity maturity model, Security Starters and Security Practitioners, are essential within the cybersecurity journey of an organization.
During these steps of the cybersecurity maturity model, cybersecurity practitioners are focusing on establishing the basics of cybersecurity within their organizations. Nearly every aspect of a company’s operations is now touched by technology. This reliance introduces new risks, however, as cyberattacks become more sophisticated and widespread. A breach can lead to data loss, reputational damage, and financial losses, among other impacts. This is why it is essential for organizations to put the basics of cybersecurity in place.
The Security Investors, Promoters and Leaders steps on the other hand focus on containment, management and anticipation of threats. These steps require medium to advanced security expertise, to manage incidents, operate a successful threat intelligence program or manage and monitor alerts in a Security Operation Center.
If you can positively ascertain that you are moving from Step 2 – Security Practitioner into Step 3 – Security Investor, then your organization is likely ready to start using cyber deception. By doing so, you can significantly reduce the risk of a successful attack.
Ready to build a Deception Program?
At Lupovis we help organizations build their deception capabilities and obtain contextual threat intelligence in real-time on adversaries. Get to know more about Lupovis, contact us now.
22 August 2022 | by Xavier Bellekens
Speak to an Expert
Whether you have a specific security issue or are looking for more information on our Deception as a Service platform, simply request a call back with one of our security experts, at a time that suits you.


