Eight reasons Deception Technology should be part of your cybersecurity efforts
19 May 2022 | by Xavier Bellekens
The need to consistently review your business’ cybersecurity is no longer optional. Regardless of the size of your company, you must regularly gauge the ability of your business to withstand cyberattacks and protect intellectual property and assets.
While this can seem overwhelming, there are more options available now, than ever before.
As well as enforcing robust, company-wide IT policies and taking the time to upskill your team, you can improve your cyber defense by making use of a wealth of advanced technologies and platforms that have been designed to detect, deter and distract cyber attackers.
One such technology that should play a crucial role in your cybersecurity efforts is deception technology.
What is Deception Technology?
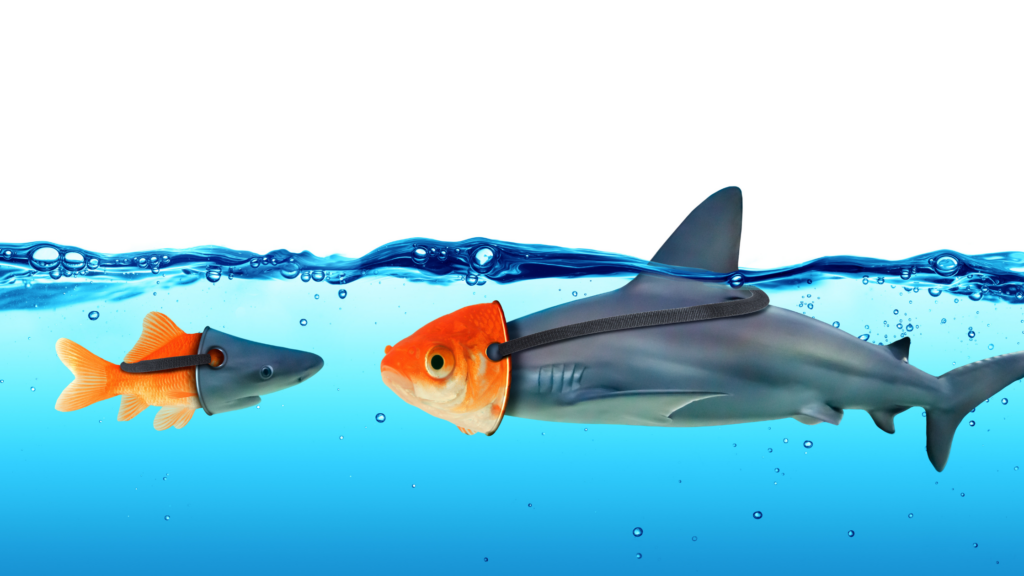
Deception technology, or cyber deception as it’s otherwise known, is precisely what it sounds like: technology aimed at preventing an attacker from creating significant damage when they attempt to hack into your network.
Deception technology works by creating decoys that mimic the legitimate technology throughout your infrastructure. This means attackers are wasting their efforts causing damage to elements that have no impact on your operating systems or organization.
Deception technology has become an essential piece of the cybersecurity puzzle. There is no security solution today that can stop every attempted attack on your network. Still, deception technology gives attackers a false sense of security, leading them to believe that they’ve gained actual access to your network, when they haven’t.
Why you should use deception techniques
If you aren’t already, your business needs to employ cyber deception technology as soon as possible. The layer of protection it adds to your existing security solution is more than worth it.
1. Cyber Deception puts your business on the offensive
While much of vulnerability management is defensive and reactive – scan for vulnerabilities, patch areas for weakness, respond to a breach – deception technology gives you the ability to turn the tables on your cyber adversaries by tricking them into revealing themselves and wasting their time and efforts on non-lures.
Essentially, their efforts are entirely futile, and all the while, your organization runs as usual.
The best part? Your SOC and threat intelligence teams gain information on the latest attack vectors, and tactics, techniques and procedures attackers use. They also gain time to respond.
2. It’s completely automated
Deception technology runs automatically, without the need for manual input, which means you can focus on running an efficient cybersecurity campaign without burning out your human resources.
With the cybersecurity industry being notoriously overworked, and a skills shortage increasing year-on-year, having a technology in place that will improve your security posture without exacerbating the staff issue is incredibly useful.
3. Deception technology enables you to fight Zero-Day attacks
Zero-day attacks, whereby a hacker manages to exploit a vulnerability before software developers can find a fix, are among the most challenging cyber-attacks to spot, and the fallout can be potentially devastating.
Attackers can use a multitude of techniques to spread malware that affects company data, programs, and computers, but with deception technology in play, they won’t get that far. Deception will allow you to detect attackers, collect data from the human attacker’s point of view ahead of an attack, and in turn use this actionable threat intelligence to better protect your network and discover gaps.
4. It can reduce alert fatigue
Cybersecurity tools often boast real-time alerts and notifications, which, while effective, can exhaust, overwhelm and distract your security team. This is particularly the case if you’re receiving lots of false positives from your SIEM.
Deception technology is not built to detect security problems through traffic analysis. Instead, it flags alerts when decoys are triggered (when access to a faux system has been attempted). This limits false information, or false positives, giving your security team a chance to breathe and pay attention to the alerts that really matter.
5. Deception technology helps you to better understand your cyber attackers
Understanding how cyber attackers work is crucial to predicting future attacker behavior, and, in turn, being able to put in place measures to build your resilience against attack, or cyber defense.
Deception techniques provide a window into the tactics attackers deploy, and through decoys, you can understand how they gather information, such as the attack vectors they try to use.
Keeping an eye on what is happening in real-time and assessing the nature of an attack helps security teams identify how hackers intend to enter your network. While you’re building up better forms of defense in those areas, you can put further decoys in place and then shut down the attack when you feel you’ve gathered enough information on your adversary. You can also use technologies such as moving target defense, to fend lateral movement, with high interaction honeypots and map the movement against Mitre Shield and Mitre ATT&CK.
6. It gives you broad coverage
Deception tools can efficiently work in every corner of your organization.
Deception detects problems in all corners of the network and systems, including areas that might typically work as blind spots. Deception technology even extend to the cloud.
It’s important to note that deception technology covers the entire cyber kill chain, from exploitation through to data loss. Though no technology is perfect, deception comes incredibly close.
7. Cyber deception is available to all businesses
One of the best aspects of deception technology is that it’s accessible to everyone.
From small businesses and startups to major corporations, you can run deception software with minimal effort and without breaking the bank. This fact alone is a significant perk because every business (and its clients) deserves stellar protection from attackers.
8. Deception technology helps prevent attacks
Cybercrime has become so sophisticated that even if your business has advanced vulnerability scanners and a fast and effective remediation solution in place, you cannot guarantee you’ll avoid a breach.
With deception technology, while cybercriminals can still attack, any damage to your systems is minimised because you have an active defense in place.
Not only that, but the decoys give you the tools needed to figure out how to prevent future attacks on your networks. Preventing cyberattacks is the future of keeping our sensitive information safe.
Cyber deception technology is a valuable tool that should be in every IT team’s arsenal. Don’t prevent your team from truly protecting your systems. Contact us today to learn more about how we can help you put cyber deception to work for your organization.
19 May 2022 | by Xavier Bellekens
Speak to an Expert
Whether you have a specific security issue or are looking for more information on our Deception as a Service platform, simply request a call back with one of our security experts, at a time that suits you.


