What is IP Intelligence?
29 December 2022 | by Xavier Bellekens

We have talked about intelligence in a variety of context, from threat intelligence to contextual intelligence with cyber deception. However, intelligence is about data and one of the easiest information to obtain is an IP address. Hence, the overview of IP Intelligence.
OSINT
Open-Source Intelligence (OSINT) is an effective and cost-savings intelligence gathering approach that has become increasingly important in the modern digital landscape. OSINT relies on publicly available information, ranging from search engines to public records, to allow organizations to increase their awareness of potential threats. By leveraging such open sources of data, companies can gain valuable insights into their own environment, as well as the activities and strategies of their competitors.
Additionally, this type of intelligence gathering plays an important role for organizations in obtaining insights on international events. Thus, investing in tools and training for personnel skilled in collecting and sorting through relevant information can provide a distinct advantage for any organization looking to better understand the contemporary operating environment.
Any cybersecurity team, whether offensive or defensive, must include OSINT. OSINT will always include IP intelligence data because the Internet is based on IPs, thus it doesn’t matter if you use it to find sensitive information about your assets that has been inadvertently exposed or to gather information for penetration testing. At the network level, IP addresses power all of its services, protocols, and the products we use every day.
What is IP Intelligence?
IP intelligence is a broad term that encompasses various purposes and technologies related to the use of an IP (Internet Protocol) address. From locating an IP address to learning information about a user’s internet behavior, IP intelligence capabilities are crucial for many aspects of modern digital communication. Some common applications for IP intelligence include providing enhanced analytics for web or mobile traffic, anticipating cybercrime activity, identifying unfair competition such as click fraud, developing targeted marketing campaigns and more. Basically, IP intelligence gives organizations the insight they need to make data-driven decisions and gain meaningful insights into online users.
What is IP Intelligence in cybersecurity?
In the context of cybersecurity, IP intelligence refers to the use of IP addresses and other related information to detect and prevent cyber threats. This can include identifying the location of an attacker or suspicious activity, as well as blocking malicious traffic from reaching its intended target.
One way that IP intelligence is used in cybersecurity is through the implementation of firewall rules. Firewalls are security systems that monitor and control incoming and outgoing network traffic based on predetermined security rules. These rules can be based on IP addresses, allowing administrators to block traffic from specific locations or block traffic to and from certain IP addresses.
IP intelligence can also be used to track the location of an attacker or suspicious activity. By analyzing the IP addresses of incoming traffic, cybersecurity professionals can identify the geographic location of an attacker and take appropriate action to prevent further damage.
Another use of IP intelligence in cybersecurity is for tracking the distribution of malware. By analyzing the IP addresses of infected devices, cybersecurity professionals can determine the origin and spread of a malware attack and take steps to prevent its further spread.
Overall, IP intelligence is an important tool in the cybersecurity arsenal, allowing professionals to detect and prevent cyber threats by analyzing and tracking the use of IP addresses. It is an integral part of a comprehensive cybersecurity strategy, helping to protect networks and devices from malicious activity.
In its purest form, IP intelligence is about obtaining information from one or multiple IP addresses.

Examples of IP intelligence data
Here is a list of metadata that can be used for IP intelligence:
- IP address: The most basic piece of metadata used for IP intelligence, an IP address is a numerical label assigned to each device connected to a computer network that uses the Internet Protocol for communication.
- Geographic location: The physical location of a device can be determined by analyzing its IP address.
- Internet Service Provider (ISP): The company that provides Internet access to a device can be determined by analyzing its IP address.
- Domain Name System (DNS) information: The DNS is a system that translates domain names (such as www.example.com) into IP addresses. Analyzing DNS information can provide insights into the location and ownership of a device.
- Autonomous System Number (ASN): An ASN is a unique identifier assigned to a group of Internet Protocol (IP) resources that are managed by a single entity. Analyzing ASN information can provide insights into the ownership and management of a device or network.
- Network topology: The physical layout of a network, including the devices and connections within it, can be determined by analyzing IP addresses and other metadata.
- Traffic patterns: The volume and direction of traffic to and from a device can be analyzed to detect unusual or suspicious activity.
- Timestamps: The time at which a device connects to the Internet can be determined by analyzing its IP address and other metadata.
- Device type: The type of device (such as a computer, smartphone, or router) can often be determined by analyzing its IP address and other metadata.
- Operating system: The type of operating system (such as Windows, MacOS, or Linux) that a device is running can often be determined by analyzing its IP address and other metadata.
- IP Reputation: IP reputation is a measure of the trustworthiness of an IP address. It is based on the history and behavior of the device or network associated with that IP address, and it is used to identify and mitigate potential threats.
- Indicators of Attacks: An IoA is any signal that marks a malicious attempt to access or make changes to a system. This may include an unusually high amount of traffic on a certain port, detection of malicious code, or unauthorized network connections.
- Indicators of Compromise: an IoC is an alert showing that the system has suffered some form of breach – either personal data has been manipulated or credentials have been stolen
What are the tools to get intelligence on IP addresses?
A number of tools can help you obtain intelligence on an IP address. There are a many of services, scripts that allow you to access IP intelligence.
- DShield : This list summarizes the top 20 attacking class C (/24) subnets # over the last three days. The number of ‘attacks’ indicates the # number of targets reporting scans from this subnet.
- TOR ExoneraTor: A database of IP addresses that have used the Tor network is kept by the ExoneraTor service. It responds to the query of whether a Tor relay was active at a specific IP address and time.
- Lupovis Prowl: Prowl is an API that allows you to send IP and in return obtain the reputation of the IP as well as indicators of attacks and indicators of compromise associated with the address. Lupovis monitors the web in real time and identifies malicious IP addresses for you.
Web based IP intelligence tools
VirusTotal : One of our favourite tools, Virustotal is an online malware and virus scanner. The power of Virustotal lies in its ability to quickly scan a file using dozens of the best and most popular malware scanners available, providing users with comprehensive results for any type of threat. Its fast and accurate results can give valuable insight into the integrity of any IP, URL, program or file being examined – vital information that can be used to keep user data secure and protect against malicious files.
BGPView: One of the key activities security researchers undertake while creating an IP profile of any organization is performing an ASN lookup to obtain complete network information, and BGPView provides all that and more. ASN information consists of information about the country, the announced prefix, the prefix name, the prefix description, the ASN, the ASN description, and the entire ASN name.

Prowl : Prowl returns intelligence information on any given IP addresses, indicates if the IP is malicious or not, as well as information such as techniques tactics and procedures associated with the IP, indicators of attacks and indicators of compromises.
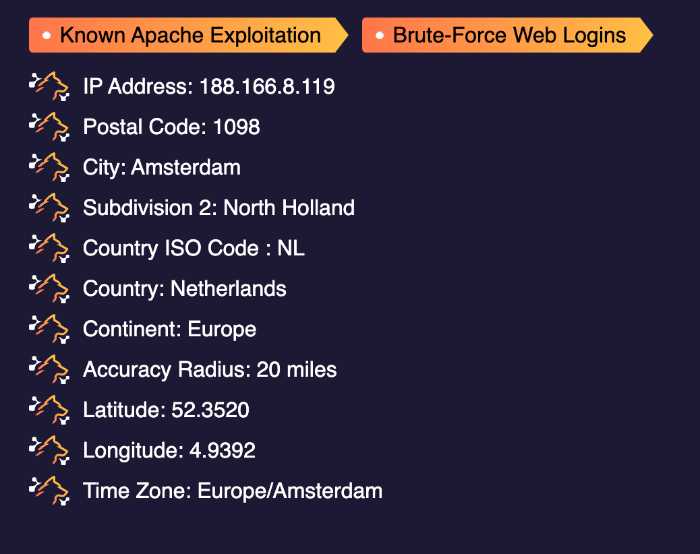
By looking at the IP information provided by Prowl, security teams can quickly determine the intentions of malicious users and block them accordingly.
For example, the IP lookup provides the country, city and postal code of any user attempting to access the network, allowing the team to not only pinpoint geographic locations but also identify if any user requests are coming from suspicious areas.
In addition, it can offer additional data which may indicate whether a user is a repeat offender or part of a larger cybercriminal collective. When used in conjunction with other security measures, such as automated rule-based blocking systems and proactive malware scanning software, IP intelligence can help bolster an organization’s security posture by automating IP blocking directly in a SIEM such as with Azure Sentinel.
Conclusion
IP addresses are an integral part of how the internet works, and as such, play a vital role in cybersecurity.
If you’re ever unsure about whether an IP address has been used maliciously or not, this post should help clear things up.
At Lupovis, we created Prowl, our enterprise-grade attack contextual intelligence tool for just this purpose – to help keep businesses safe from potential threats. Have you found this post helpful? If so, be sure to check out API website for more information on how we can help keep your business secure.
29 December 2022 | by Xavier Bellekens
Speak to an Expert
Whether you have a specific security issue or are looking for more information on our Deception as a Service platform, simply request a call back with one of our security experts, at a time that suits you.


