Identify and Prevent Reconnaissance Attacks
15 June 2022 | by Xavier Bellekens

Reconnaissance techniques are used by threat actors to gather information about a target system in order to plan a more sophisticated attack.
What is reconnaissance in cybersecurity?
Reconnaissance attacks can be defined as attempts to gain information about an organization’s systems and networks without the explicit permission of the organization. These attacks are usually carried out by threat actors who are trying to find vulnerabilities they can exploit. However, they can be very difficult to detect, as they often involve seemingly innocent activities’ reconnaissance techniques.
Reconnaissance techniques are often focused on 5 distinct steps
- Collect information and data about the target network
- Understand the network (south or north of the firewall)
- Identify active services and devices
- Discover services and open ports
- Map the network and its network services
Once the network mapped, adversaries will try to gain access to publicly available information such as
- Data, files and their content
- Users and usernames
- Relationships
- Account information
- Source code
What are the types of reconnaissance attacks?
Passive reconnaissance
Passive Reconnaissance is a method of gathering information about an organization by using various means. These include Wireshark and Shodan which allows not only see what’s going on but also harvest information for later use. We can use passive reconnaissance to gather information about an organization without sending interacting with their website or network. This type of surveillance often utilizes public resources.
The intelligence gathered from open sources is called Open Source Intelligence (OSINT). One way to gather this information are through IP addresses, domain names, email accounts, etc. You can also find out the services a server has installed. The CVEs associated with that particular piece of software will also be of interest in order for you to make an informed decision when selecting a target.
Valuable information and confidential information can be obtained from the data a company or an individual shares online. Some IT professional share pictures and information of their infrastructures on social media, for example. This initial information can help an adversary make informed guesses about the running services for subsequent steps (e.g., for social engineering purposes).
Active reconnaissance
Active reconnaissance is faster and more precise, but it’s riskier as it create more noise on the different system that can be detected by the administrators or the security team. It requires the attacker to make a connection to the system. This can range from active fingerprinting to social engineering.
Furthermore, it is often used a second step against the target , as it often includes information obtained during the passive reconnaissance steps, such as the IP address of the hosts discovered earlier.

Passive Reconnaissance Tools
Google Hacking
Google dorking, is the practice of exploiting Google search algorithms to obtain sensitive information that is not readily available. This can be done through simple queries that return results that are not intended to be seen by the public.
For example, a Google dork query might return results that include social security numbers or credit card information. It can be used to gain information, such as identity or documents, through web searches. Google dorking is also used for espionage or to gain competitive intelligence.
It is important to note that Google hacking is not a new phenomenon; it has been around since the early days of Google search. However, it has become more prevalent in recent years as Google has become more sophisticated and attackers have become more adept at exploiting its algorithms.
Shodan
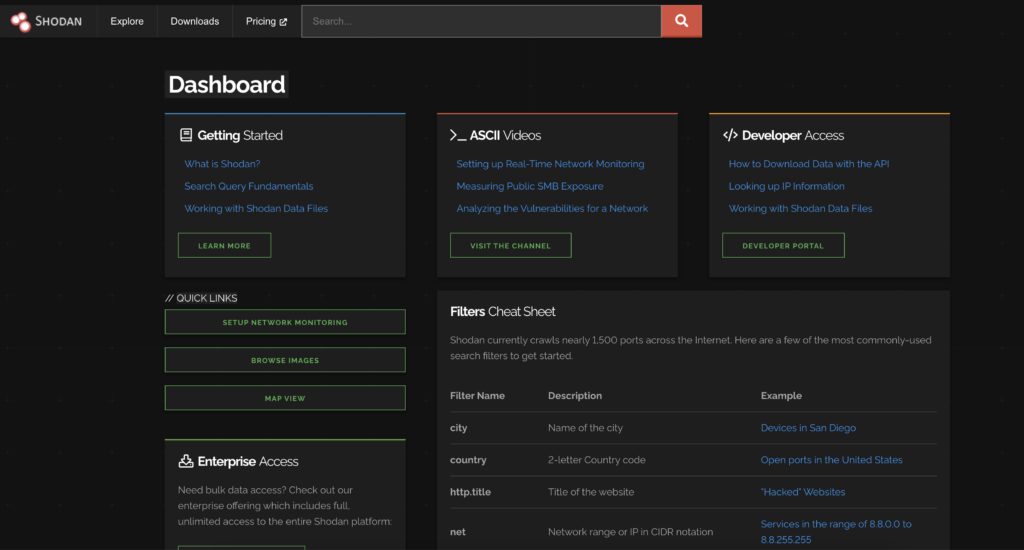
Passive reconnaissance is the process of gathering information about a target without directly interacting with it. This can be done by studying public records, observing the target from a distance, or looking for information that has been leaked online. While passive reconnaissance does not require any specialized skills or tools, it can still be very time-consuming. As a result, many people turn to Shodan as a way to speed up the process.
Shodan is a search engine that allows users to find devices and services that are connected to the internet. By entering specific keywords or filters, users can narrow their search to find exactly what they are looking for. For example, a user might search for an IP address or all webcams that are publicly accessible, or all routers that are running outdated firmware.
In addition to its main search functionality, Shodan also offers a number of tools that help users gather intelligence about their targets. These tools include a port scanner, a service detector, and a vulnerability scanner. With these tools, users can quickly gather a wealth of information about their target without ever having to directly interact with it. As a result, Shodan has become an essential tool for anyone doing passive reconnaissance.
CVE
CVE, or Common Vulnerabilities and Exposures, is a publicly disclosed cybersecurity vulnerabilities database. Its goal is to provide a reference for which risks can be identified and addressed.
CVE entries are assigned by one of several CVE Numbering Authorities (CNAs), who take responsibility for assigning identifiers to publicly disclosed cybersecurity vulnerabilities. These identifiers are used by vulnerability management systems to track and fix security issues. In addition, some CNAs also publish advisories and tools that contain information about CVE entries.
CVE is sponsored by US-CERT, part of the Cybersecurity and Infrastructure Security Agency (CISA) and can be used during the information gathering phase or to obtain information about active machines and vulnerabilities discovered by vulnerability scanners other tools.
Wireshark
Wireshark is a network analysis tool that enables you to see what’s happening on a network at a granular level. It captures and analyzes traffic in real-time, giving insights into how a network is being used and potential issues that may arise.
Wireshark can be used for both passive and active network analysis. passive network analysis involves monitoring traffic and gathering data without interfering with the operation of the network. Active network analysis, on the other hand, includes tests and troubleshooting that can disrupt network operations.
Wireshark is an essential tool for any passive and active reconnaissance once inside a network , as it provides valuable insights into network activity and can help identify network services, cyber security issues, weak passwords, unecrypted communications, known vulnerabilities, or operating system and/or active machines on small and large networks alike.
Maltego
Maltego is an OSINT and forensics application. It can be used to discover information about people, companies, organizations, etc. Maltego uses a unique technique called “graph link analysis” to reveal hidden connections between entities or find telephone numbers. This makes it a powerful tool for reconnaissance and investigation.
Maltego is available in both free and paid versions. The free version is limited in terms of features and functionality, but it is still a useful tool for many tasks. The paid version offers more features and is suitable for more complex tasks. Overall, Maltego is a powerful tool that can be used for a variety of purposes such as social engineering attacks or find information from web sources such as news articles and does it generally faster than manual searching.
Active Reconnaissance Tools
The majority of the tools are vulnerability scanners, that can be used for automated scanning or manual testing. All can be during the reconnaissance phase to scan large networks, identify information system, or obtain detailed information on the target.
Nmap and Port Scanning
Port Scanning is like knocking on doors to see if someone’s home. Running a port scan reveals which ports are open and listening (receiving information), as well as revealing the presence of security devices or identifying the version of an operating system or service. This technique can also be used by insider threats.
Nmap: Network scanning tools such as NMAP send User Datagram Protocol datagrams and/or Transmission Control Protocol segments to probe the ports of the target hosts. There are 65535 ports available. The IANA has identified certain ranges as “well-known ports,” which are assigned services by them. These standardized numbers cover 0 – 1023 and include many important network functions such as:
- Port 54 – Domain Name System (DNS)
- Port 80 – Hypertext Transfer Protocol
- Port 25 – Simple Mail Transfer Protocol (SMTP)
- Port 20 – File Transfer Protocol (FTP) for data transfer
- Port 22 – Secure Shell (SSH) protocol for secure logins
- Port 23 – Telnet protocol
Nmap is excellent at cyber reconnaissance, creating a network map and scanning larger networks.
Metasploit
Metasploit was designed to be used as an exploitation tool. It comes with a number of modules that come with ready-to-use exploits for a range of vulnerabilities and vulnerability information. However, using manual testing and a number of modules, metasploit can be used to do stealthy reconnaissance and obtain information on the target host.
Nessus
Nessus is a vulnerability scanner. Its goal is to find vulnerable services on a network or system and give a range of information about exploiting the vulnerabilites found. Nessus is an automated scanning commercial software, however the information it delivers can be a game changer during the information gathering phase.
OpenVAS
OpenVAS is another vulnerability scanner. When the Nessus became closed-source, OpenVAS was build from the final open-source version to give a free alternative. As a consequence, it has a lot of the same features as Nessus, although it misses some of the features that have been added since Nessus was first released.
Nikto
Nikto2 is an an Open Source (GPL) web server vulnerability scanner comparable to Nessus and OpenVAS that may be used for reconnaissance. Nikto scans web servers for a variety of issues, including over 6700 potentially harmful files/programs, outdated versions on over 1250 sites, and version-specific problems on over 270 servers. It also looks for server configuration elements like numerous index files. Nikto is often used during penetration testing engagement as it is relatively stealthy.
Burpsuite
Burp Suite is a web application security testing platform and graphical tool that covers the whole testing process, from initial mapping and analysis of an application’s attack surface through detecting and exploiting security flaws. Burp suite is often used in penetration testing engagements.
How to Prevent a Reconnaissance Attack
Given adversaries use reconnaissance to identify weaknesses in a system, network or organisation.
Make Reconnaissance Harder
Organizations rely on reactive attack detection and response tools. This often results in their inability to identify reconnaissance attacks. There are however several steps organizations can take to limit an adversary’s reconnaissance efforts and to disrupt an attacker’s planning.
Phase I
The first phase of an attack is all about learning as much information possible. This will include IP addresses, DNS names, domains, subdomains, potential vulnerabilities.
Phase II
Phase two will be building a map for your business. Adversaries will be learning all they can about the people involved in it. This includes their names, job titles and contact information. This will also using google dorcks extensively to find files, content or information that can help during the actual attack in the final phase.
Phase III
In phase three, the adversary will validate the information obtained in the previous phases, and might include techniques such as social engineering to obtain new information interacting directly with employees based on the initial information obtained.
Phase IV
Once enough reconnaissance has taken place, available resources have been exhausted, adversaries will test the cyber security of the oganisation.
The largest weakness in any organization is its predictability. No matter how careful you are, there will always be vulnerabilities that an attacker can exploit to cause major damage and disruption within your company’s operations. Furthermore, every organization creates data, and data can be mined.
Deploying Campaigns
Limiting the ability of attackers to perform reconnaissance is essential. This can be achieved by deploying deception campaigns outside of your network. Deception environment are fake systems and services that are designed to look like real systems. They are used to lure attackers in and then track their activity. By deception, we can stop reconnaissance attacks before they happen.
- The first advantage is that you will now gain the upper hand. By providing information you control to an adversary you essentially control the adversary path.
- The second advantage that is not negligeable is that you will also be able to find out when someone is looking for information on your organization.
- Deploy breadcrumb information leading threat actors towards a deceptive zone, where they will provide you with threat intelligence.
- Provide deception assets to the adversary, these will generate high fidelity information such as Indicator of Attacks (IOA) and Indicator of Compromise (IOC).
Cyber deception technology has been shown to be effective in stopping reconnaissance attacks. In a study by the SANS Institute, it was found that deception were able to detect 91% of attempted attacks and prevented adversaries and threat actors from progressing further.
This is because attackers will often give up if they cannot find what they’re looking for quickly. By deception, we can make it appear as though our systems are much more vulnerable than they actually are, making the attacker’s job much harder and ultimately deterring them from continuing.
The bottom line is that reconnaissance techniques and reconnaissance attacks are difficult to detect and thwart with current technologies. However, by implementing deception tactics into your security strategy you can gain valuable insights into the early stages of a cyber attack, allowing you to better protect your organisation from potential harm.
If you’re interested in learning more about how our next-generation threat intelligence and deception platform can help you detect and respond to reconnaissance attacks, please don’t hesitate to contact us. We would be happy to answer any questions or discuss how we can work together to keep your business safe online.
15 June 2022 | by Xavier Bellekens
Speak to an Expert
Whether you have a specific security issue or are looking for more information on our Deception as a Service platform, simply request a call back with one of our security experts, at a time that suits you.


