Iranian Scanning Activity Spike Observed Across the Internet in February 2026
12 March 2026 | by Xavier Bellekens
Iranian scanning activity increased noticeably across the internet in February 2026 according to telemetry collected from the Lupovis sensor network. While background scanning is constant on the internet, the volume and timing of this activity stood out compared to the baseline normally observed.
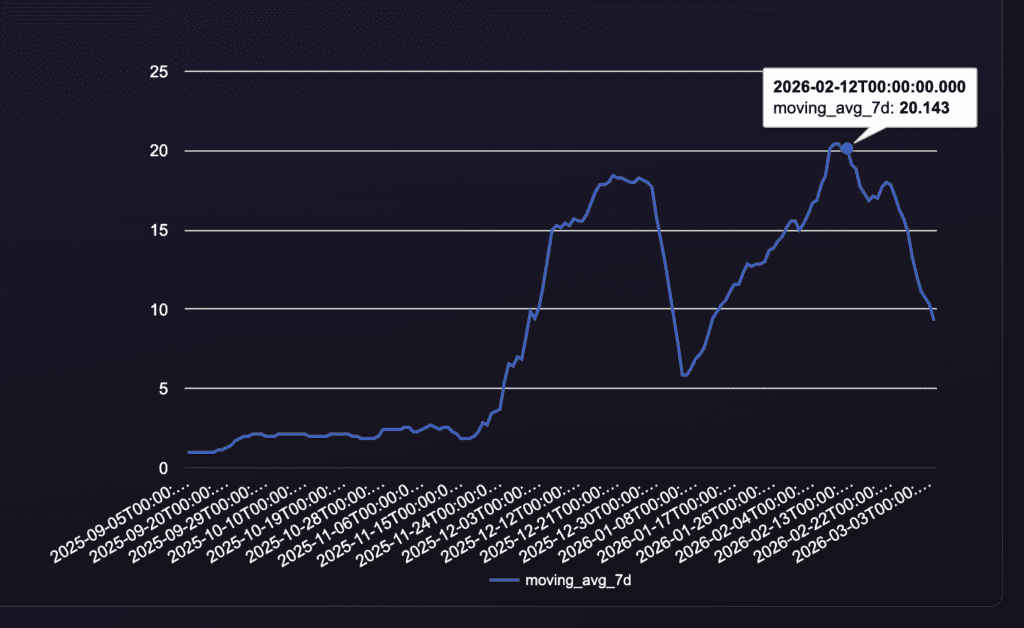
The increase began in early February and accelerated rapidly, reaching a peak around the middle of the month. During this period, Lupovis sensors recorded a significantly higher number of unique attacker IP addresses associated with infrastructure located in Iran. The requests observed during this time were primarily probing attempts directed at publicly accessible services, indicating automated reconnaissance activity designed to identify exposed or vulnerable systems.
This type of scanning activity is common when attackers attempt to map the internet for potential targets before exploitation begins.
Spike in Iranian Scanning Activity
The Iranian scanning activity rose sharply during the first half of February. The number of unique attacker IP addresses participating in the activity increased well beyond the levels typically observed from the same region.
Across Lupovis sensors, the pattern of requests suggested the use of automated scanning frameworks distributing reconnaissance tasks across multiple nodes. Rather than focusing on specific organizations, the traffic appeared to sweep across large address ranges and multiple networks.
This behavior is consistent with large-scale internet reconnaissance campaigns that attempt to identify vulnerable systems as quickly as possible. Attackers often distribute scanning across many IP addresses in order to increase speed and avoid detection.
Such spikes are frequently observed when a vulnerability becomes incorporated into automated scanning tools. Once integrated into attacker frameworks, scanning activity can increase dramatically as operators search for unpatched systems across the global internet.
Geographic Targeting of the Activity
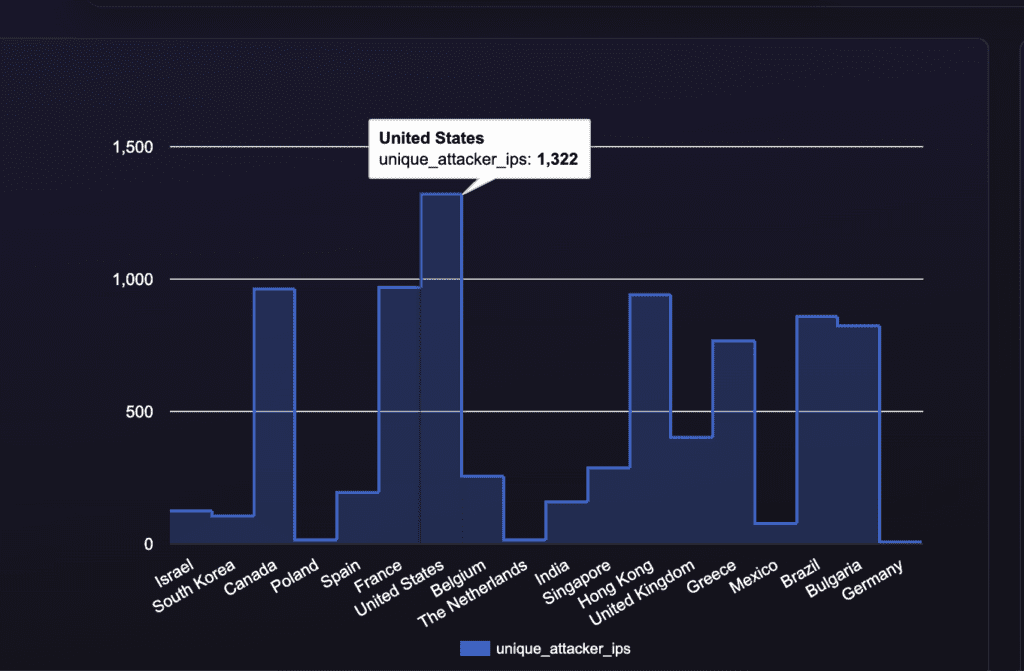
Analysis of destination networks shows that a large portion of the Iranian scanning activity observed during this period targeted infrastructure located in the United States.
This pattern is not unusual. A significant share of globally accessible enterprise infrastructure is hosted within the United States due to the concentration of cloud providers, enterprise networks, and hosting platforms located there.
Because of this concentration, large-scale reconnaissance campaigns frequently focus on US-based infrastructure simply because it represents a large portion of the exposed attack surface on the internet.
Although the majority of the observed traffic targeted US networks, other countries were also scanned at lower volumes.
Possible Drivers Behind the Activity
There are several plausible explanations for the spike in Iranian scanning activity observed in February.
One possibility is the integration of newly disclosed vulnerabilities into automated scanning frameworks. When exploit code becomes available or vulnerabilities receive widespread attention, attackers often deploy automated tools to scan the internet for systems that remain unpatched.
These tools allow attackers to quickly identify potential targets before organizations have fully applied patches or mitigation measures.
Another explanation is that the activity may have been part of a broader reconnaissance campaign intended to build a target inventory. Threat actors frequently conduct wide-scale scans to map internet-facing services and infrastructure before launching more focused intrusion attempts.
In many cases, scanning campaigns occur days or weeks before any exploitation attempts are detected.
Both scenarios are consistent with the patterns observed in Lupovis telemetry.
And the patterns observed by Symantec Threat Hunters seeing Seedworm: Iranian APT on Networks of U.S. Bank, Airport, Software Company during the same period.
Activity Declines Toward the End of February
Toward the end of February, the volume of Iranian scanning activity began to decline and eventually returned closer to baseline levels.
This reduction could indicate several possibilities. The scanning campaign may have completed its initial enumeration phase, operators may have rotated their infrastructure, or reconnaissance efforts may have shifted toward other networks or geographic regions.
Large internet-wide scanning campaigns frequently appear and disappear over short periods as attackers adjust their operational priorities.
Why Monitoring Scanning Activity Matters
Monitoring spikes in reconnaissance activity across the internet provides valuable early warning signals for defenders.
When scanning activity increases rapidly, it often indicates that attackers are actively searching for vulnerable systems at scale. These signals can provide organizations with early indicators that certain vulnerabilities or services are attracting increased attacker attention.
By identifying these shifts early, security teams can prioritize patching, monitor logs for exploitation attempts, and strengthen defenses before widespread exploitation occurs.
Continuous monitoring of internet-wide scanning behavior helps security teams understand when vulnerabilities transition from theoretical risk to active attacker interest.
Conclusion
The spike in Iranian scanning activity observed in February 2026 highlights how quickly automated reconnaissance campaigns can expand across the internet.
Although the activity declined toward the end of the month, the telemetry illustrates how attackers use distributed scanning infrastructure to rapidly probe large portions of the global attack surface.
Understanding these patterns helps defenders anticipate attacker behavior, respond faster to emerging threats, and reduce the window of opportunity between vulnerability discovery and exploitation.
Security teams should track exploitation signals and review advisories published by CISA, MITRE and other threat intelligence sources.
12 March 2026 | by Xavier Bellekens
Speak to an Expert
Whether you have a specific security issue or are looking for more information on our Deception as a Service platform, simply request a call back with one of our security experts, at a time that suits you.


